From Supply Chains to Cartels: Mapping China’s Overlap with the Illicit Economy
Over the past decade, China’s expanding influence across Latin America, Central America, and Africa has increasingly overlapped with regions dominated by entrenched illicit networks. This is not necessarily a story of direct coordination—but it is one of convergence, where state-driven investment, weak oversight, and transnational criminal systems operate in parallel, creating conditions where influence and illicit economies can grow side by side with limited resistance.
Over the past year, I’ve spent a considerable amount of time writing about China—not as an academic expert, but as someone who has worked in and around the country long enough to recognize patterns as they emerge. That work has ranged from analyzing China’s latest AI developments, like GLM-5—not just as a model, but as a strategic signal—to examining the erosion of civil liberties in Hong Kong through cases like Jimmy Lai. I’ve also explored Chinese-linked cyber leaks and what they reveal about a broader global espionage architecture, as well as the Chinese Communist Party’s long-standing doctrine of irregular warfare, often described as the “Three Warfares.” Taken together, these aren’t isolated topics—they point to a more coordinated and evolving strategy.
What ties these threads together—and what has become harder to ignore in recent years—is the scale and consistency of China’s efforts to expand its influence well beyond its borders. From large-scale infrastructure investments across Africa to strategic footholds in Latin America and Central America, Beijing’s approach appears deliberate, long-term, and multifaceted. In some cases, this shows up in visible ways—port development, energy projects, and increasing involvement in critical transit points like the Panama Canal ecosystem. In others, it is far less visible, unfolding through cyber operations, information shaping, and economic dependencies that are only fully understood in hindsight.
At the same time, there has been a growing recognition—both in policy circles and in the broader public discourse—that these efforts are not isolated initiatives, but part of a broader strategy. Whether viewed through the lens of competition, security, or economic alignment, the question is no longer whether this expansion is happening, but how it is being executed, and to what end.

Infrastructure & Strategic Access
China’s global expansion is often discussed in terms of infrastructure—ports, railways, energy projects, and digital networks stretching across Africa, Latin America, and Central America. These initiatives, frequently tied to the Belt and Road framework, are typically framed as economic development. And in many cases, they are. But infrastructure is never just infrastructure.
Ports, logistics hubs, and transportation corridors do more than move goods—they shape access, control, and visibility. In regions where governance is uneven or institutions are under strain, these projects can take on additional significance. Strategic assets—whether near major shipping lanes, resource-rich territories, or key transit chokepoints—become embedded within environments that already host complex informal and illicit economies.
Nowhere is this more relevant than in parts of Latin America and Central America, where longstanding trafficking routes overlap with emerging investment zones. Maritime infrastructure, for example, sits at the intersection of global trade and illicit movement. The same ports that facilitate legitimate commerce can, under the right conditions, be exploited for smuggling, trafficking, and parallel supply chains.
The point is not that infrastructure projects are designed for illicit use—but that they exist within ecosystems where illicit networks are already deeply entrenched. When strategic investment meets weak oversight, the result is a layered environment where state-backed development and criminal enterprise operate in parallel—sometimes intersecting, often invisible to one another, but sharing the same physical and logistical terrain.
Illicit Supply Chains
If infrastructure defines the physical landscape of global influence, supply chains define how that influence moves—quietly, persistently, and often out of sight. Over the past decade, one of the most consequential developments in this space has been the fragmentation of production and distribution networks tied to illicit goods. These are no longer localized operations. They are transnational systems, built on the same efficiencies and redundancies that power legitimate global trade.
A clear example can be seen in the evolution of synthetic drug supply chains. Rather than relying on a single point of origin, production has become distributed. Chemical precursors are manufactured in one region, shipped through intermediaries, refined elsewhere, and ultimately distributed through established trafficking networks. Each stage is compartmentalized, reducing risk while increasing resilience. The result is a system that is harder to disrupt precisely because it mirrors the structure of modern global commerce.
Within this model, China has frequently been identified as a major source of precursor chemicals—materials that are legal in isolation but become dangerous when diverted into illicit production. Regulatory tightening in recent years has shifted some of this activity, but not eliminated it. Instead, it has adapted. New intermediaries, new routes, and new jurisdictions have emerged, reinforcing the idea that these systems evolve faster than the policies designed to contain them.
What makes this dynamic particularly significant is not just the origin of materials, but the convergence of supply chains. The same shipping networks, financial channels, and logistical frameworks that support legitimate trade are often leveraged—sometimes knowingly, often opportunistically—by illicit actors. In regions where oversight is inconsistent, these parallel systems can operate with minimal friction, embedded within the broader flow of global commerce.
Again, the issue is not one of direct coordination, but of structural overlap. When state-linked industrial capacity, global distribution networks, and entrenched trafficking organizations all operate within interconnected systems, the line between legal and illegal becomes less distinct. It is within that ambiguity that modern illicit economies thrive—adaptive, decentralized, and increasingly difficult to isolate from the very systems that enable global growth.
Financial & Money Movement Ecosystems
If supply chains explain how illicit goods move, financial systems explain how value moves—and, more importantly, how it is concealed, transformed, and reintegrated into the global economy. Modern illicit networks are not just trafficking operations; they are sophisticated financial enterprises, designed to move large volumes of capital across borders with minimal detection.
One of the most persistent features of this ecosystem is trade-based money laundering. By manipulating invoices, mispricing goods, or routing transactions through layered intermediaries, illicit actors are able to disguise the movement of funds within otherwise legitimate commercial activity. This approach is particularly effective because it does not rely on secrecy alone—it relies on scale. Billions of dollars in global trade flow every day, and within that volume, small distortions are difficult to isolate without highly coordinated oversight.
Over time, informal financial networks have also evolved to complement these methods. In various regions, underground banking systems—operating parallel to formal institutions—facilitate the rapid movement of funds without the same regulatory scrutiny. These systems often intersect with diaspora communities, cross-border commerce, and, increasingly, digital platforms. The lines between formal banking, shadow finance, and emerging fintech are becoming more fluid, creating both efficiency and vulnerability.
China’s role within this landscape is complex. As a central node in global manufacturing and trade, it sits at the intersection of vast financial flows. This positioning does not inherently imply complicity, but it does mean that Chinese-linked financial channels, commercial networks, and payment systems can become embedded—directly or indirectly—within broader money movement ecosystems. In some documented cases, Chinese underground banking networks have been linked to laundering proceeds for transnational criminal organizations, illustrating how global connectivity can be leveraged in unintended ways.
What emerges from this is not a single pipeline, but a layered system—formal and informal, regulated and unregulated, transparent and opaque—operating simultaneously. In environments where enforcement is uneven or incentives are misaligned, these layers can interact in ways that allow illicit capital to circulate with relative ease. As with infrastructure and supply chains, the defining characteristic is not coordination, but convergence: a financial architecture where legitimate commerce and illicit enterprise share the same pathways, often indistinguishable until examined closely.
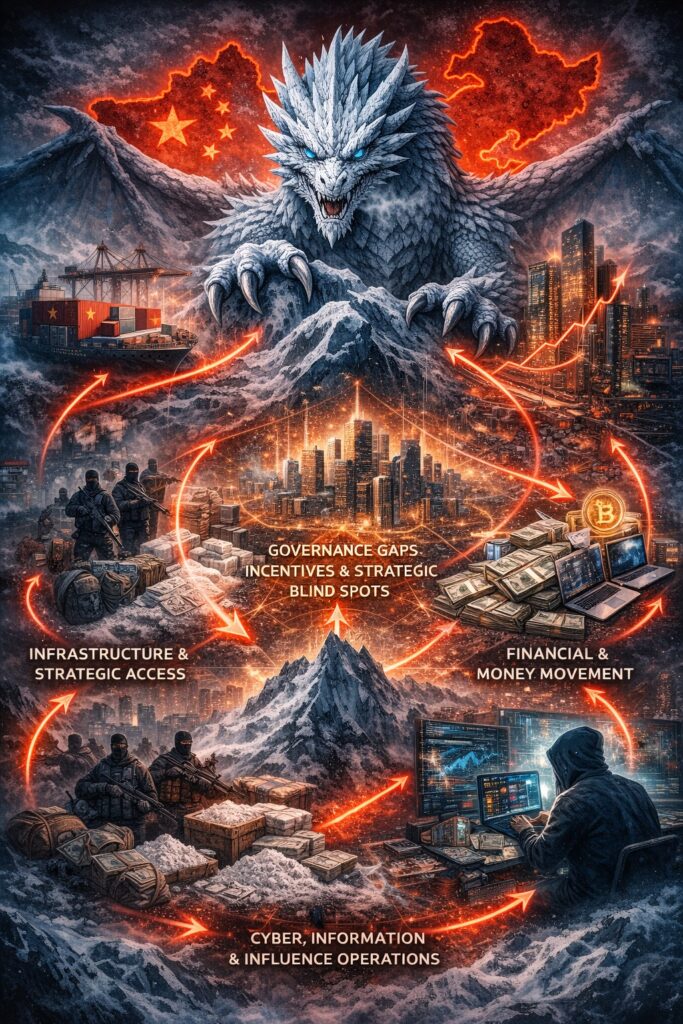
Cyber, Information, and Influence Operations
Beyond physical infrastructure and financial systems lies a less visible—but equally consequential—layer of influence: the digital and informational domain. This is where access becomes insight, and insight becomes leverage. Over the past several years, China’s approach to cyber operations, data collection, and narrative shaping has drawn increasing scrutiny, not only for its scale, but for its integration into broader strategic objectives.
Cyber capabilities serve multiple functions simultaneously. They enable intelligence gathering, support economic positioning, and provide pathways into critical systems—both public and private. At the same time, information operations shape perception: influencing how events are interpreted, how policies are debated, and how narratives take hold within both domestic and international audiences. Together, these efforts reflect a model of engagement that extends well beyond traditional diplomacy or trade.
This dynamic extends beyond infrastructure and into the realm of perception itself. Open-source reporting and government assessments in recent years have increasingly pointed to Chinese-linked influence operations aimed at shaping public opinion abroad. These efforts often focus on amplifying favorable narratives, suppressing criticism, or subtly influencing how political and economic issues are framed within target countries. In some cases, analysts have identified campaigns tied to online networks and state-aligned actors that engage with political discourse—including commentary around policies, leadership, and, at times, the broader information environment surrounding elections and candidates. While the scale and impact of these efforts can vary, they reflect a broader pattern: influence is not limited to physical or economic domains, but extends into how populations interpret events, institutions, and choices.
This is not a theoretical framework. In practice, cyber and information operations are ongoing and active across many of the same regions where China has expanded its physical and economic presence. In parts of Africa, Latin America, and Central America, digital infrastructure projects, telecommunications partnerships, and data systems have created new points of access and influence. These systems are often introduced as development tools—and in many cases, they deliver real value—but they also expand the digital footprint through which data can be collected, monitored, or shaped over time.
This approach aligns closely with what Chinese strategists have long described as the “Three Warfares”: psychological warfare, media warfare, and legal warfare. Rather than relying solely on kinetic or overt confrontation, this doctrine emphasizes shaping the environment—perceptions, rules, and information—before conflict ever becomes visible. In that sense, cyber operations are not isolated tools; they are part of a broader strategy designed to influence outcomes without direct engagement.
When viewed alongside infrastructure, supply chains, and financial systems, the digital layer completes a more comprehensive picture. Access to ports enables movement. Access to supply chains enables production. Access to financial systems enables capital flow. And access to data—combined with the ability to shape information—enables influence. Each layer can function independently, but together they form an ecosystem where visibility is uneven, accountability is fragmented, and the boundaries between state activity, commercial interest, and other actors become increasingly difficult to define.
Governance Gaps, Incentives, and Strategic Blind Spots
By the time infrastructure, supply chains, financial systems, and digital influence are viewed together, a more consistent pattern begins to emerge. These are not isolated developments, nor are they easily explained through a single lens of intent or coordination. Instead, they point to environments where multiple systems—state-driven, commercial, and illicit—operate simultaneously, each driven by its own incentives, but often sharing the same space.
In many of the regions where this convergence is most visible, governance is uneven. Regulatory frameworks may exist on paper but lack consistent enforcement. Institutions tasked with oversight are often constrained—by resources, political realities, or competing priorities. Within these gaps, both legitimate and illicit actors find room to operate. What begins as economic development or strategic investment can, over time, intersect with informal economies that are already deeply embedded in the local landscape.
This is where incentives begin to matter more than intent. For governments seeking growth, infrastructure and foreign investment can take precedence over aggressive enforcement actions that might disrupt economic momentum. For local power structures, stability—however defined—can outweigh efforts to dismantle entrenched networks. And for external actors, maintaining access and influence may not always align with pushing for systemic reform. None of these dynamics require explicit coordination, but together they create conditions where enforcement becomes inconsistent and selective.
The result is not necessarily a deliberate tolerance of illicit activity, but a form of strategic ambiguity. In these environments, certain problems persist not because they are endorsed, but because addressing them fully would introduce friction—economic, political, or strategic—that few stakeholders are willing to absorb. Over time, this ambiguity can function as a kind of passive enabler, allowing parallel systems to coexist with limited disruption.
Seen through this lens, the issue is less about any single country or actor, and more about the structure of the system itself. When influence, access, and economic interdependence expand faster than governance and accountability, gaps will form. And within those gaps, networks—licit and illicit alike—adapt, expand, and reinforce their position. The question is not whether this dynamic exists, but how long it can persist before the consequences become more visible—and more difficult to ignore.
Closing Perspective
The convergence outlined here does not point to a single actor pulling strings behind the scenes. It points to something more complex—and potentially more consequential. A world in which global influence, economic expansion, and illicit networks are no longer separate domains, but overlapping systems shaped by shared infrastructure, shared incentives, and shared blind spots.
China’s role in this landscape is significant, not because it controls every element within it, but because of the scale and reach of its presence across so many of these interconnected layers. Where that presence intersects with weak governance, entrenched criminal networks, and evolving digital ecosystems, the result is a form of coexistence that is difficult to measure, harder to regulate, and easy to underestimate.
For policymakers, analysts, and anyone paying attention, the challenge is not simply to identify these overlaps, but to understand them. Because the risk is not always in what is explicitly coordinated—but in what is allowed to persist, adapt, and grow in the spaces where systems converge and accountability falls behind.